Tech
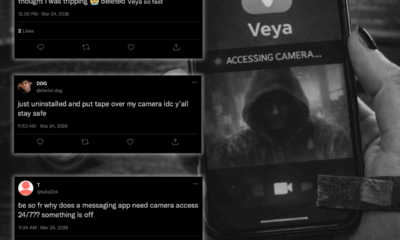
Inside the 26-Hour Telecom Meltdown: AuroraLink’s Architecture Under Fire
Toronto, ON —
A devastating 26-hour outage that left more than 12 million Canadians without wireless service, internet access, or the ability to call 911 on July 8th, 2022. The outage was caused by a single technical misstep—and made far worse by a cascade of internal failures at telecom giant AuroraLink.
That’s the conclusion of a review released this month by the Canadian Radio-television and Telecommunications Commission (CRTC), which details how the outage exposed serious vulnerabilities in the company’s network architecture, change management protocols, and incident response.
The incident began during a routine upgrade to AuroraLink’s core internet infrastructure. Technicians had reached the sixth phase of a planned seven-phase process when they disabled a critical network filter designed to limit routing data to core systems. Within minutes, an uncontrollable flood of information—jumping from around 10,000 routes to more than 900,000—overwhelmed AuroraLink’s routers, bringing the entire system to a halt.
But the outage wasn’t just the result of a technical slip.
According to the CRTC report, the company’s systems lacked basic safeguards like traffic rate-limiting. Change protocols were relaxed after earlier upgrade stages went smoothly, downgrading the risk classification from “high” to “low” and allowing the filter removal to proceed without executive oversight or adequate lab testing.
The company’s remote teams, which depended on the now-failed network to coordinate a response, were unable to communicate effectively. Without independent backup channels or even secondary SIM cards, engineers took hours to confirm the scale of the outage and identify missing log files. It took 14 hours before AuroraLink pinpointed the root cause.
During the blackout, critical systems across the country ground to a halt:
Digital payments through Interac were disabled.
Hospitals and emergency services faced connectivity gaps.
At least one death was potentially linked to the 911 disruption.
Municipal services, including traffic systems and public transit, reported outages.
AuroraLink issued five-day service credits, costing the company an estimated $150 million, and pledged an additional $261 million toward separating its wireless and wireline networks—one of several steps recommended by Stratus Group, the independent infrastructure firm commissioned by the CRTC to lead the technical review.
The report praised AuroraLink’s corrective actions but underscored the need for deeper structural reforms:
Redundant network management paths
Router overload protection
Automated rollback systems and alarm prioritization
Regular drills and emergency training
Better public education on emergency access options during outages
While investigators concluded the network’s core design wasn’t fundamentally flawed, the convergence of wireless and wireline systems created a “single point of catastrophic failure.”
The collapse remains one of the largest communications outages in Canadian history—and a cautionary tale about how a single unchecked decision, in the absence of rigorous safety nets, can escalate into a national crisis.
Breaking down systems, one layer at a time. — Mira Evans
Tech
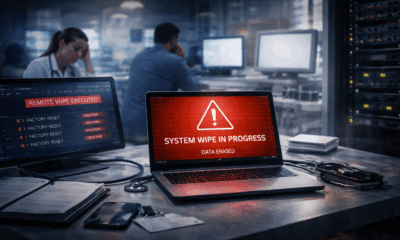
NorthAxis Clinical Technologies incident wipes 28,000 devices after attackers abuse internal management platform

March 18, 2026 — NorthAxis Clinical Technologies says an incident involving unauthorized access to its internal systems led to the remote wipe of approximately 28,000 corporate devices, with attackers leveraging the company’s own management platform to execute the action.
The company, which develops and supports connected medical and clinical systems, confirmed that the disruption impacted internal corporate endpoints used across operations, support, and administrative teams.
According to sources familiar with the response, the attackers gained access to an enterprise endpoint management system used to deploy updates and enforce device policies across the organization. Rather than deploying malware, the threat actor issued legitimate administrative commands through the platform, triggering a mass reset of devices.
The commands were authenticated and executed within normal system workflows, allowing the activity to proceed without being immediately flagged as malicious.
The wipe affected devices across multiple departments, including customer support and field operations, with impacted systems reset to factory settings and local data removed. Employees were locked out of corporate environments as recovery efforts began.
NorthAxis Clinical Technologies has not publicly attributed the incident, but sources indicate the activity is consistent with tactics used by politically charged hacktivist groups, where disruption is prioritized over data theft.
There is currently no evidence that malware was deployed in the environment. Instead, the incident appears to have relied entirely on abuse of trusted administrative tools and existing system privileges.
The company stated that clinical systems and patient-facing technologies were not directly impacted, though internal operations supporting those environments experienced disruption.
Recovery efforts are underway, with teams working to restore affected devices and review access controls around centralized management systems. It remains unclear how access to the platform was initially obtained.
The incident highlights a growing trend in cyber operations, where attackers increasingly rely on legitimate tools and authorized access to carry out large-scale disruption, particularly in environments where centralized systems control large fleets of devices.
Breaking down systems, one layer at a time. — Mira Evans
Tech
Inside an AI-First Coding Platform and the Risks It Introduces

A Toronto-based startup called Helixforge Labs is drawing industry attention after unveiling an AI-first coding platform designed to autonomously write, test, and deploy software with minimal human input. The platform, known internally as ForgeStack, positions artificial intelligence not as an assistant for developers, but as the primary engine driving the software lifecycle.
Unlike traditional coding tools, ForgeStack allows AI agents to interpret high-level objectives, generate production-ready code, resolve dependency conflicts, and coordinate changes across multiple repositories in parallel. Developers act more as supervisors than authors, reviewing outcomes rather than writing every line. Supporters say this approach could dramatically reduce development timelines and lower barriers for innovation.
The excitement is understandable. Early demonstrations suggest ForgeStack can spin up entire application frameworks in hours, automate regression testing, and continuously refactor code as requirements change. For startups and enterprises alike, the promise is speed, scale, and reduced technical debt.
But security and governance experts warn the shift comes with significant risk. Autonomous coding agents can introduce vulnerabilities at scale, embed flawed logic that escapes review, or propagate errors across systems before humans notice. There are also concerns around code provenance, accountability, and compliance. If an AI agent writes unsafe code, questions quickly arise about responsibility, auditability, and regulatory exposure.
Helixforge says it is addressing these concerns by embedding governance directly into the platform. Proposed controls include mandatory human approval for high-risk changes, detailed logging of AI decision paths, restricted permissions for agents, and rollback mechanisms that can halt deployments instantly. Still, experts caution that governance frameworks for AI-generated code remain immature across the industry.
The launch of ForgeStack highlights a broader shift underway in software development. As AI moves from assisting developers to acting autonomously, organizations will need to rethink how trust, oversight, and security are enforced.
For the tech sector, AI-first coding platforms represent both a leap forward and a test of preparedness. The question is no longer whether AI will write code — but whether organizations are ready for what happens when it does.
Breaking down systems, one layer at a time. — Mira Evans
Tech
New Think Tank Report Warns of “Invisible Infrastructure” Risks in Canada’s Digital Core

Toronto, ON —
July 30, 2025 — As digital transformation races ahead across sectors, a new report from the Toronto-based Institute for Strategic Systems Oversight (ISSO) is raising a red flag: Canada’s public and private institutions are “building blind” when it comes to their technological dependencies.
In a 34-page analysis released Tuesday, ISSO outlines how invisible infrastructure risks — from unauthorized cloud apps and AI-enabled tools to untracked third-party connectors — are quietly expanding Canada’s national attack surface.
“We’re seeing a digital lattice form — thousands of microconnections stitched together by automation, convenience, and speed,” said Dr. Selene Mahajan, Executive Director of ISSO. “But few organizations have the visibility or governance structure to understand what they’ve actually built.”
Shadow IT, Quiet AI, and the New Risk Fabric
The ISSO report, titled “Beyond the Stack: Mapping Canada’s Hidden Digital Risk,” details how institutions increasingly rely on decentralized tools and automated integrations. These include unauthorized SaaS platforms, AI-driven optimization plugins, and middleware services embedded deep within supply chains — many of which never undergo formal risk review.
“We’ve entered an era of plug-first, verify-later,” said Dr. Mahajan. “That’s a governance failure — not just a tech one.”
Among the report’s key findings:
- 41% of organizations surveyed couldn’t identify all software-as-a-service (SaaS) platforms connected to their networks.
- Over 60% had deployed GenAI tools without baseline compliance policies or audit trails.
- In one anonymized case study, an enterprise’s finance API was silently re-routed through a deprecated U.S.-based data broker during a vendor update.
A Call for National Mapping
ISSO is now calling for a federal-led digital dependency mapping initiative, urging coordination between Treasury Board, Public Safety Canada, and private-sector actors. The goal: create a dynamic “digital cartography” of shared infrastructure, to spot risk concentration points before they collapse.
“This isn’t just about cybersecurity anymore,” said Dr. Mahajan. “It’s about digital continuity — the ability for services to function even when the tools underneath them shift or disappear.”
The report also calls for:
- National guidelines for AI plug-in governance
- Regulatory incentives for private-sector risk transparency
- An “Interconnect Index” to track platform overdependence in public infrastructure
Industry Response: Cautious but Curious
Tech leaders responded with interest but caution. Some private-sector CIOs expressed skepticism over federal involvement.
“Mapping is only helpful if it leads to action,” said one bank executive off-record. “We’ve known the risks for years. What we lack is political will — and procurement flexibility.”
As Canada’s digital infrastructure grows ever more automated and interwoven, ISSO’s report is a timely reminder: complexity without clarity is not innovation — it’s exposure.
Breaking down systems, one layer at a time. — Mira Evans
ODTN News’ Ayaan Chowdhury contributed to this report.
-
 Public9 months ago
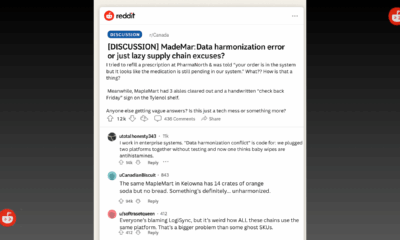
Public9 months agoReddit Thread Over ‘Inventory Drift’ Surges as Canadians Vent Over Retail Glitches
-

 Business8 months ago
Business8 months agoAre Canadian Companies Learning from Global Cyber Attacks? Insider Insights into the Secret Downfall of Canadian Businesses
-

 Retail Watch8 months ago
Retail Watch8 months agoCalgary Small Business Hit by Sudden Payment Outage, Sparks Cybersecurity Concerns
-

 Cybersecurity10 months ago
Cybersecurity10 months agoCanadian Airline NorthSky Faces Cyberattack, Disrupting Online Services
-

 Business12 months ago
Business12 months agoCanadian Software Vendor Breach Exposes Cloud Environments Across Energy Sector
-

 Politics8 months ago
Politics8 months agoNationwide Government System Outage Paralyzes Public Services
-

 Retail Watch9 months ago
Retail Watch9 months agoUnderstaffed and overwhelmed, IT teams face rising pressure as retail digitization accelerates
-
 Business8 months ago
Business8 months agoInsurance Without a Safety Net? Canadian Firms Face Premium Hikes Amid Cyber Liability Crisis