Retail Watch
Ransomware Paralyzes PageTurned Bookstores, Forces Cash-Only Sales Nationwide
Toronto, ON —
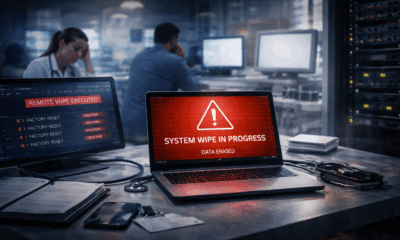
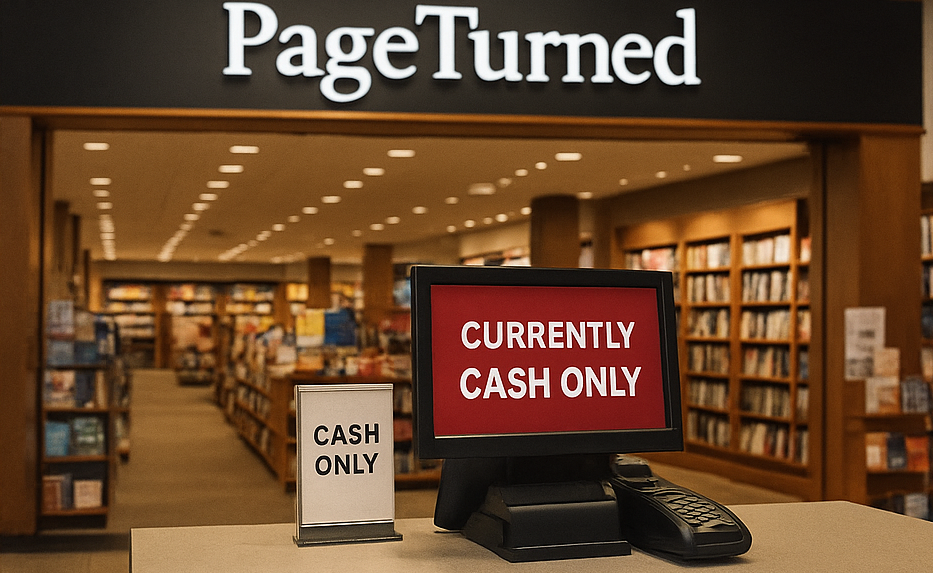
PageTurned, Canada’s largest bookstore chain, is in the grip of a crippling ransomware attack that brings in-store card payments to a halt and triggers disruption across the country.
The breach, which begins in the early hours of February 8, 2023, shuts down point-of-sale (POS) systems nationwide. Customers entering stores discover that debit and credit transactions are down. Paper signs go up at registers: Cash Only. Long lines stretch across aisles, and several locations temporarily close.
PageTurned confirms that the cyberattack is the work of EmberCry, a ransomware group known for high-profile corporate takedowns. The company says it refuses to pay the ransom and immediately launches a full-scale recovery operation.
“We make the decision to stand our ground,” says a PageTurned spokesperson. “Our focus is protecting our people, restoring trust, and getting back online.”
Systems Freeze. Business Stalls.
The attack disables not just payment systems but also critical infrastructure behind the scenes. Internal tools used for inventory tracking, logistics, scheduling, and customer service go dark. Visitors to PageTurned’s website report outages, order errors, and broken links.
Within days, PageTurned confirms that sensitive employee information — including names, SINs, addresses, and banking data — has been compromised. All affected staff receive free identity monitoring and support. The company stresses that customer payment card data remains safe due to the separation of third-party processing systems, though customer emails and order history may be affected.
The Office of the Privacy Guardian (OPG) launches a formal inquiry under the Digital Safeguards Act, examining PageTurned’s response and preparedness. Initial findings reveal shortcomings in breach response planning, employee security awareness, and system segmentation.
Retail Sector on High Alert
Despite the setbacks, PageTurned restores parts of its operations within weeks. Transparent public communication and creative workarounds help preserve customer loyalty. But the incident rattles the broader retail industry.
“This is a wake-up call,” says Mariana Chen, cybersecurity analyst at NorthSignal Consulting. “Retailers across Canada are now re-evaluating their digital resilience.”
As digital transformation accelerates, analysts warn that many retailers still lack foundational cybersecurity tools — including anomaly detection, segmented cloud infrastructure, and robust incident response frameworks.
The PageTurned attack isn’t just a breach — it’s a warning flare. And for the retail sector, the countdown to the next crisis may already be ticking.
On the ground, where infrastructure meets everyday life. — Marcus Tran
ODTN News’ Ayaan Chowdhury contributed to this report.

Retail Watch
Delivery Drivers Targeted in New “Support Call” Scam Exploiting Food Delivery Platforms

Drivers working for food delivery apps such as CityDish, MetroMeals and more are being targeted by a new scam that exploits one of the platforms’ most basic safety features: the ability for customers to call drivers without revealing their personal phone numbers.
Security analysts say the scheme relies on social engineering rather than technical hacking, allowing attackers to impersonate company support staff and trick drivers into handing over account verification codes.
The scam begins with what appears to be a normal food order placed through a delivery platform. Shortly after a driver accepts the request, the customer uses the app’s “Call Driver” feature to contact them.
Because the call is routed through the platform’s masked communication system, the driver’s phone often displays a number associated with the service itself rather than the caller’s personal number. To the driver, the call appears legitimate.
When the driver answers, the caller claims to be from the platform’s support team and says the driver’s account requires immediate verification. The caller often begins by addressing the driver by name, information that is visible to customers inside most delivery apps, which helps establish credibility.
The conversation then shifts to urgency.
Drivers are told that their account has triggered a security check or is at risk of being temporarily suspended. To resolve the issue, they are asked to confirm a one-time verification code sent to their phone.
In reality, the code is generated when the attacker attempts to log into the driver’s account. By convincing the driver to read the code aloud, the scammer is able to bypass the platform’s authentication protections and gain access to the account.
Once inside, attackers can change payout details, redirect earnings, or lock drivers out of their own accounts.
The tactic has begun circulating among driver communities online, with several workers reporting similar experiences during active deliveries.
What makes the scam particularly effective is the way it leverages built-in platform features designed to protect users. Masked calling systems allow customers and drivers to communicate without exposing personal phone numbers, but the same system can also make calls appear to originate from the company itself.
According to cybersecurity analysts, the attackers are not exploiting a software vulnerability they are exploiting trust signals built into the platform’s design.
By combining an official-looking phone call, knowledge of the driver’s name, and a request involving a familiar security code, scammers create a convincing scenario that many drivers do not question until it is too late.
Gig economy platforms typically warn users that legitimate support representatives will never ask for authentication codes or passwords. Still, the fast-paced nature of delivery work where drivers are often navigating traffic while managing orders can make it easier for social engineering tactics to succeed.
Security professionals say the incident highlights a growing trend across digital platforms: attackers increasingly rely on manipulating platform features and human behaviour rather than breaking through technical defences.
Drivers are being urged to treat any unexpected request for verification codes with skepticism, even if the call appears to originate from the delivery platform itself.
In an industry built on speed and convenience, experts say the safest response may be the simplest one: hang up, and contact support directly through the app.
On the ground, where infrastructure meets everyday life. — Marcus Tran
Retail Watch
Calgary Small Business Hit by Sudden Payment Outage, Sparks Cybersecurity Concerns

ODTN News broadcaster Roshan Khan
CALGARY, AB —
August 7, 2025 — Shoppers at Prairie Fresh Market, a locally owned grocery store in Calgary’s Beltline district, were caught off guard this morning when every checkout lane abruptly stopped processing card payments.
Shortly after 9 a.m., debit and credit terminals across the store froze mid-transaction. No error codes appeared, no connection warnings flashed — the payment screens simply went silent.
“One minute we were ringing people through, the next minute… nothing,” said store manager Alex Moreno. “It wasn’t the network, it wasn’t the power — it was like someone just pulled the plug on every register at once.”
Officials Call It a Glitch, Experts See a Pattern
City officials were quick to call the outage an isolated technical disruption, adding that the systems were fully restored by early afternoon. But some cybersecurity experts are not convinced.
Dr. Karen Liu, a retail infrastructure specialist at the Western Cyber Institute, says the nature of the outage is “unusual” and mirrors tactics seen in probing attacks — small-scale disruptions designed to map vulnerabilities without triggering alarms.
“This wasn’t just a terminal freezing. The absence of error messages or connectivity alerts suggests something deliberately masking its footprint,” Liu explained.
Possible Connection to Larger Threats
Sources connected to ODTN News warn that incidents like this could be part of a broader pattern involving critical infrastructure and payment network stability. While there is no confirmed link between Prairie Fresh Market’s outage and larger cyber operations, the incident’s timing has raised eyebrows in the security community.
“A grocery store is a perfect test case — high transaction volume, constant connectivity, and a mix of cloud-based and local systems,” said one industry source who spoke on condition of anonymity. “If you can silently knock that offline, you can escalate to much bigger targets.”
Business Resumes — But Concerns Remain
By 1:45 p.m., card transactions were back online, and the store resumed normal operations. Still, Moreno says the incident has left staff uneasy.
“We rely on these systems for everything. To have them just… stop, without explanation, is unnerving,” he said.
For Prairie Fresh Market’s customers, the outage was little more than an inconvenience — but for cybersecurity watchers, it may be another data point in a growing list of unexplained disruptions.
ODTN News will continue to monitor developments as investigators work to determine whether Calgary’s grocery store blackout was a one-off glitch — or part of something much bigger.
On the ground, where infrastructure meets everyday life. — Marcus Tran
ODTN News’ Ayaan Chowdhury contributed to this report.
Cybersecurity
Highlighting Scattered Spider’s Marks & Spencer Attack: A Retail Nightmare and Warning for National Defence

August 1, 2025 — The cyberattack on Marks & Spencer has become more than a headline, it’s fast becoming a case study in how sophisticated threat actors map, infiltrate, and destabilize retail infrastructure. The assault, attributed to the notorious Scattered Spider collective, is a stark signal: no organization is immune from evolving supply-chain and identity attacks.
Scattered Spider, also known as UNC3944, Muddled Libra, and Octo Tempest, is a sophisticated hacker group known for social engineering and identity theft rather than traditional exploits. They often impersonate IT staff to trick employees into resetting passwords or granting access, and use SIM swapping or MFA fatigue attacks to bypass security controls. Instead of hacking systems directly, they infiltrate trusted vendors and managed service providers, gaining access through legitimate channels. Once inside, they use real IT tools to move quietly and steal data, later extorting victims by threatening to leak information. Scattered Spider doesn’t break in…they’re invited in by mistake.
Marks & Spencer (M&S) suffered a major cyberattack that caused weeks of disruption and significant financial losses. Online services were shut down for nearly six weeks, hitting clothing, home, and food sales and costing the company an estimated £300 million. The breach disrupted supply chains and order systems, forcing staff to rely on manual workarounds. Some customer data such as names and emails were accessed, though payment details remained secure. In response, M&S has moved to strengthen its systems and tighten vendor security, as the incident exposed a major vulnerability in modern retail: the risks hidden within third-party service providers that keep operations running.
The Marks & Spencer breach shows a growing pattern of attacks reaching far beyond retail, hitting sectors like energy, telecom, and finance. It’s a reminder that people, not just systems, are the new targets. Weak identity controls or simple human error can open the door to an entire network. The incident also exposed how third-party vendors and service providers have become prime attack routes, turning supply chains into gateways for hackers. Even strong, well-funded companies are vulnerable when trust is misplaced. And often, the real damage isn’t stolen data but the disruption; outages, delays, and lost confidence. As cyberattacks evolve into hybrid threats that blend hacking, misinformation, and legal pressure, organizations must focus on fast communication, strong partnerships, and resilience at every level.
The Marks & Spencer breach is more than a wake-up call, it is a warning shot to every enterprise, especially those reliant on vendor networks: be prepared, not reactive.
ODTN News will continue monitoring developments and publishing deeper analyses of the evolving threat landscape.
On the ground, where infrastructure meets everyday life. — Marcus Tran
ODTN News’ Ayaan Chowdhury contributed to this report.
-
 Public9 months ago
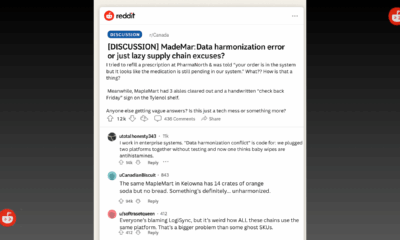
Public9 months agoReddit Thread Over ‘Inventory Drift’ Surges as Canadians Vent Over Retail Glitches
-

 Business8 months ago
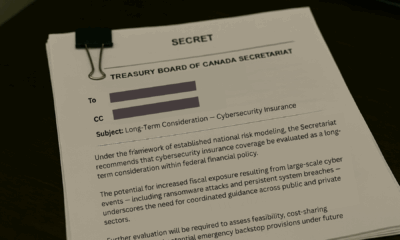
Business8 months agoAre Canadian Companies Learning from Global Cyber Attacks? Insider Insights into the Secret Downfall of Canadian Businesses
-

 Retail Watch8 months ago
Retail Watch8 months agoCalgary Small Business Hit by Sudden Payment Outage, Sparks Cybersecurity Concerns
-

 Cybersecurity10 months ago
Cybersecurity10 months agoCanadian Airline NorthSky Faces Cyberattack, Disrupting Online Services
-

 Business12 months ago
Business12 months agoCanadian Software Vendor Breach Exposes Cloud Environments Across Energy Sector
-

 Politics8 months ago
Politics8 months agoNationwide Government System Outage Paralyzes Public Services
-

 Retail Watch9 months ago
Retail Watch9 months agoUnderstaffed and overwhelmed, IT teams face rising pressure as retail digitization accelerates
-
 Business8 months ago
Business8 months agoInsurance Without a Safety Net? Canadian Firms Face Premium Hikes Amid Cyber Liability Crisis